A few months ago our Attack Vector Miner discovered a new botnet, that we simply call „Hello Peppa botnet”. Now, this botnet welcomes the new year in a new mask.
Specifics of this botnet
Its behaviour stayed the same, like what we mentioned in the case of the Hello Peppa:
- Checks backdoors which remained from a previous infection.
- Uses the Mozilla/5.0 User Agent
- The most targeted URLs are:
| /7788.php |
| /8899.php |
| /9678.php |
| /conflg.php |
| /db.init.php |
| /db__.init.php |
| /db_session.init.php |
| /mx.php |
| /qq.php |
| /s.php |
| /sheep.php |
| /w.php |
| /wc.php |
| /wshell.php |
| /wuwu11.php |
| /xshell.php |
| /xw.php |
| /xx.php |
The only difference is in the Post Data
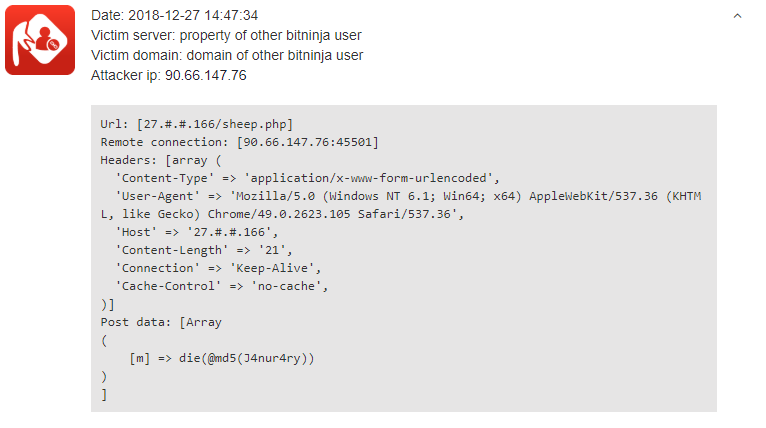
The Post Data is changed from die("Hello, Peppa!”) to die(@md5(J4nur4ry). The hackers couldn’t even write "January" correctly - they made a little typo with the extra r. Here is an example log from our Dashboard:
January became earlier
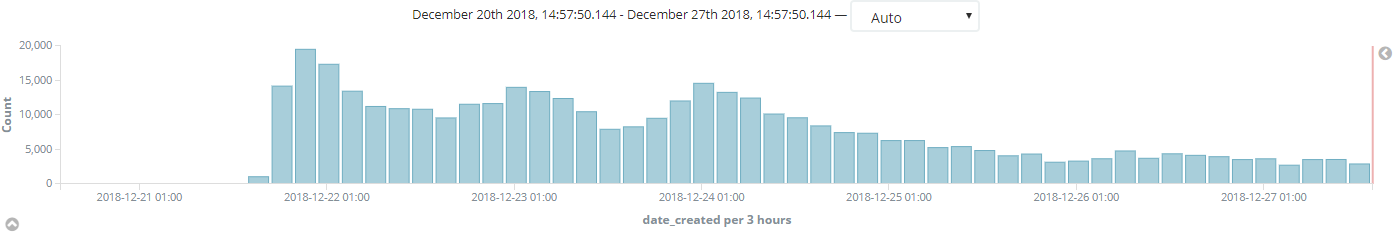
The botnet is a bit impatient because the „January botnet” didn’t wait until January; it started on 21st December. This chart shows you clearly how it was spreading:
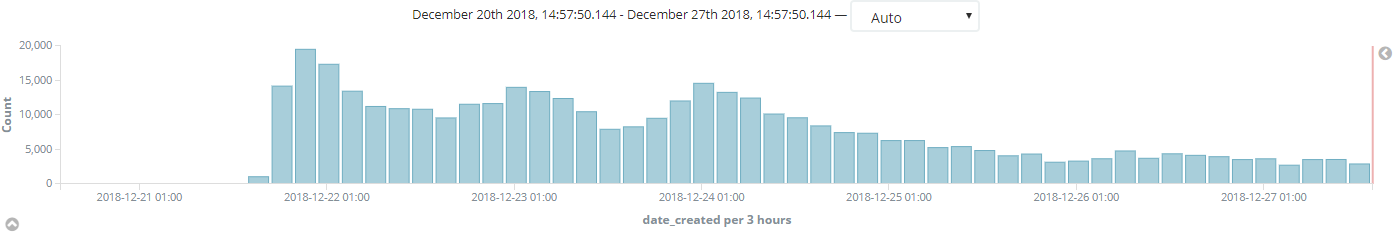
It shows the number of stopped „January botnet” attacks between 20th Dec and 27th Dec 2018. During this period, we perceived almost 400,000 attempts.
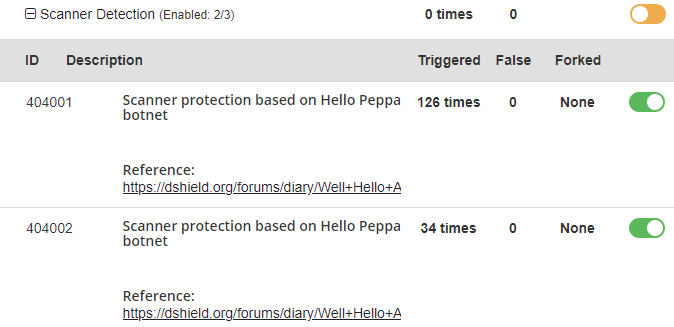
With BitNinja your servers are protected
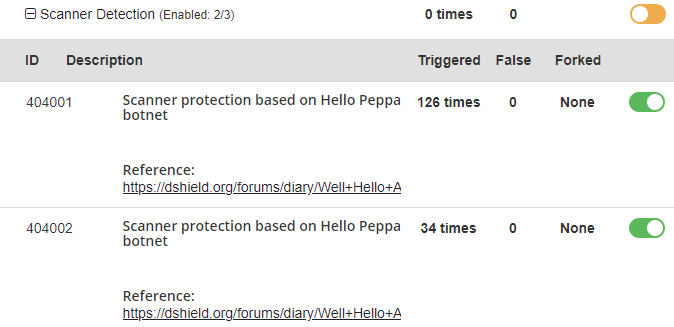
You don’t have to worry, as the 404001 and 404002 WAF rules (which are part of the safe minimum ruleset) provide you powerful protection against this botnet.
So, if the WAF 2.0 is enabled on your servers, instead of having a headache because of the „January botnet”, all you have to do is open a bottle of champagne and celebrate the start of the new year! Let’s welcome January while your servers are safe. 😉
Have questions? Ninjas are always glad to help you, so feel free to leave a comment under this article or contact us at info@bitninja.io.