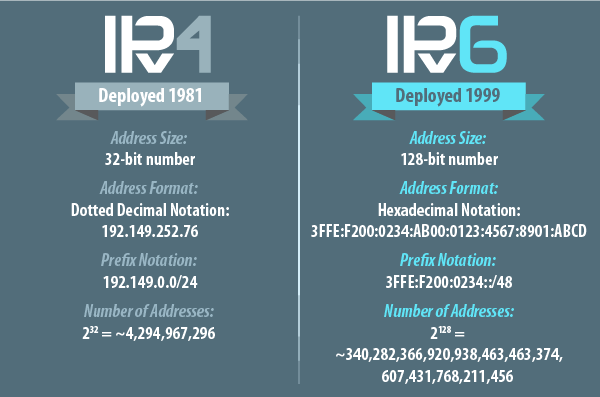
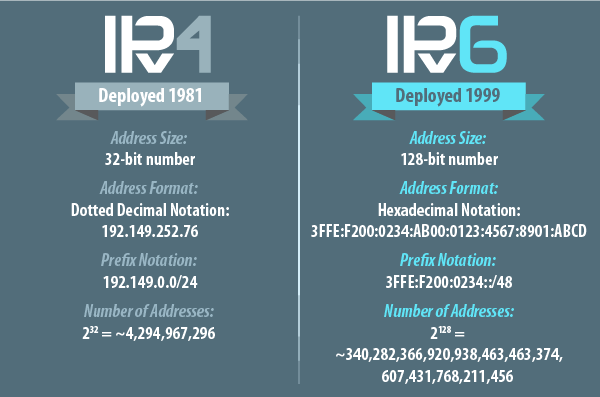
Did you know that using IPv6 on your server can completely bypass all your security? On Linux, there are separate kernel stacks, and separate mechanisms to filter traffic for the original IPv4 traffic and for IPv6. The kernel module responsible for this filtration is called ipfilter, and there is an other module called ipfilter6 for IPv6 traffic filtration.
The bad news is, you can have any rules for IPv4, it won’t help you against IPv6 traffic. Recently there was a case where BitNinja’s general port honeypot module started to catch malicious packets on an interface which had only one IPv4 address from the private address space of 10.* How could it happen? After investigating the case deeper, we realized that this interface also had a public IPv6 address, so it was publicly available through IPv6 without any protection.
Is your server vulnerable?
You can easily find out by running this command:
# ip -6 addr
1: lo: mtu 16436
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: mtu 1500 qlen 1000
inet6 xxxx:xxxx:x:xxxx:6ff:fe9b:3e85/64 scope global dynamic
valid_lft 2591998sec preferred_lft 604798sec
inet6 fe80::64dc:6ff:fe9b:3e85/64 scope link
valid_lft forever preferred_lft forever
3: eth1: mtu 1500 qlen 1000
inet6 fe80::f4d2:e3ff:fe30:f14a/64 scope link
valid_lft forever preferred_lft forever
Only the global scope ipv6 addresses make your server reachable from outside, but it worth to take a look, as we saw all the same attacks coming through IPv6 as on IPv4.
If you don’t use ipv6, it is the safest to disable this functionality. To disable IPv6 on your Linux server, use these two commands as root:
echo 1 > /proc/sys/net/ipv6/conf/all/disable_ipv6
Don’t forget to add this line to rc.local to run it on every boot as the command above only temporarily disables IPv6, until the next reboot.