WordPress is the most known CMS in the world currently (WordPress runs 32% of the entire internet), we hear that it is the easiest CMS to handle, to install and to use.
Taking all these information into account, we would think that it is safe as a house. Wrong! It might be easy to use, but for this exact reason, it is easy to hack. As it is free, there are many free plug-ins which are usually not up to date, creating weak points. Hackers always tend to exploit vulnerabilities in Plugins, Themes and WP Core. There are many parts where WordPress should be strengthened, now I would like to highlight one.
The WordPress default login page
Why you should change the original login page? The answer is simple, everyone will know about your login page, makes it easy to attack with brute force.
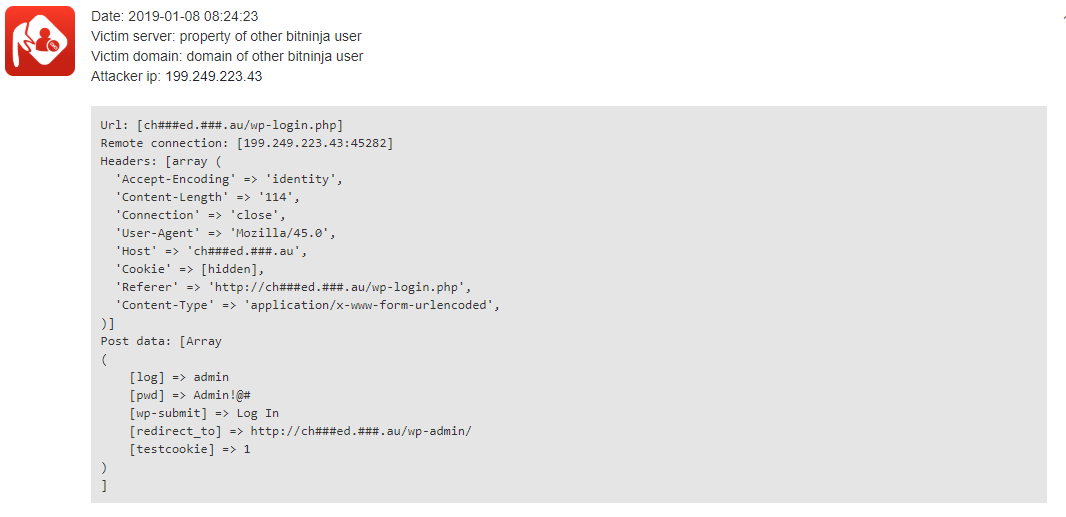
How does it look like in BitNinja logs?
Most people know (and bots as well) that if you wish to log in to a WordPress it will be either wp-login or wp-admin. In some cases wp-admin is just a redirection from wp-login just like in this case : wp-login.php?redirect_to=http%3A%2F%2Ftest.com%2Fwp-admin%2F&reauth=1
If someone knows the login page, I am sure they will try to brute-force it just like as in the example below:
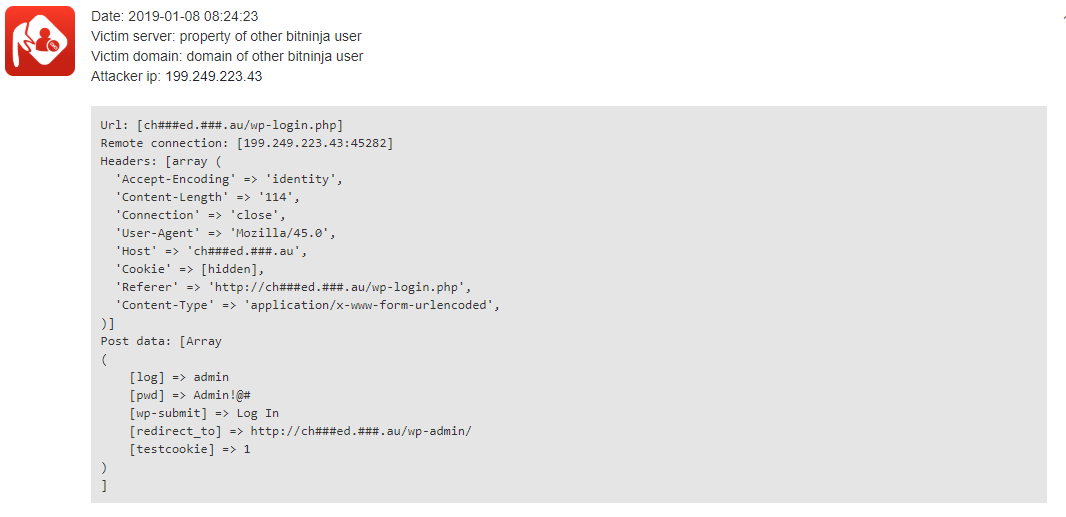
Clearly visible that someone tried to break in through the wp-login page. Our last year summary about the most common attack types of 2018 shows that in the top 10 WordPress is the most attacked with the WordPress Brute-force Login Attempt (BNVL-2018-0009) and Redirect Vulnerability in WordPress's WP Login Plugin (wp-login.php) (BNVL-2018-0008)
The way to change the wp-login page
As everyone knows it is not a good thing to pile up a lot of plugins in WordPress, however, if you wish to keep your site as safe as you can, then you can consider this as an essential one.
There are plenty of plugins which would do the work in order to change the WordPress default login page, but the WPS Hide Login is the most mentionable. Currently, it has over 300.000 installs, high ratings, and constant updates. This plugin will help you to change the login URL without changing the files in your WordPress core code. It will intercept page requests and makes the admin and wp-login page inaccessible.
The last important information snippet is that you should never ever include the original login page to the robots.txt, you might think that robots do respect this file, however, it is the other way around, they use every piece of information from that file in order to attack your site or server.
Are you protected already?
With BitNinja you are already protected thank to our WAF rules (especially to our WordPress rules) and SenseLog module, which has been created for your own security. If you wish to dig deeper just check out our article series about how you can protect your WordPress sites with BitNinja.